Reading: Textbook Chapter 13
Chapter 13: Future Trends in Information Systems
Learning Objectives
Upon successful completion of this chapter, you will be able to:
• describe future trends in information systems.
Introduction
Information systems have evolved at a rapid pace ever since their introduction in the 1950s. Today, devices that we can hold in one hand are more powerful than the computers used to land a man on the moon. The Internet has made the entire world accessible to us, allowing us to communicate and collaborate with each other like never before. In this chapter, we will examine current trends and look ahead to what is coming next.
Global
The first trend to note is the continuing expansion of globalization. The use of the Internet is growing all over the world, and with it the use of digital devices. The growth is coming from some unexpected places; countries such as Indonesia and Iran are leading the way in Internet growth.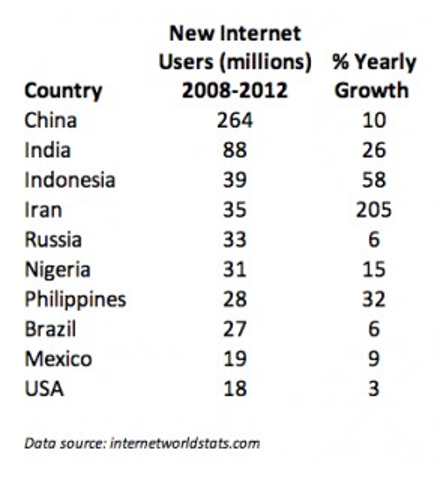
Global Internet growth, 2008–2012. (Source: Internet World Stats)
Social
Social media growth is another trend that continues. Facebook now has over one billion users! In 2013, 80% of Facebook users were outside of the US and Canada.1 Countries where Facebook is growing rapidly include Indonesia, Mexico, and the Philippines. 2
Besides Facebook, other social media sites are also seeing tremendous growth. Over 70% of YouTube’s users are outside the US, with the UK, India, Germany, Canada, France, South Korea, and Russia leading the way.3 Pinterest gets over 50% of its users from outside the US, with over 9% from India. 4 Twitter now has over 230 million active users. 5 Social media sites not based in the US are also growing. China’s QQ instant-messaging service is the eighth most-visited site in the world.6
Personal
Ever since the advent of Web 2.0 and e-commerce, users of information systems have expected to be able to modify their experiences to meet their personal tastes. From custom backgrounds on computer desktops to unique ringtones on mobile phones, makers of digital devices provide the ability to personalize how we use them. More recently, companies such as Netflix have begun assisting their users with personalizations by making suggestions. In the future, we will begin seeing devices perfectly matched to our personal preferences, based upon information collected about us in the past.
Mobile
Perhaps the most impactful trend in digital technologies in the last decade has been the advent of mobile technologies. Beginning with the simple cellphone in the 1990s and evolving into the smartphones and tablets of today, the growth of mobile has been overwhelming. Here are some key indicators of this trend:
• Mobile device sales. In 2011, smartphones began outselling personal computers.7
• The number of smartphone subscribers grew at 31% in 2013, with China leading the way at 354 million smartphone users.
• Internet access via mobile. In May of 2013, mobile accounted for 15% of all Internet traffic. In China, 75% of Internet users used their smartphone to access it. Facebook reported that 68% of its active users used their mobile platform to access the social network.
• The rise of tablets. While Apple defined the smartphone with the iPhone, the iPad sold more than three times as many units in its first twelve months as the iPhone did in its first twelve months. Tablet shipments now outpace notebook PCs and desktop PCs. The research firm IDC predicts that 87% of all connected devices will be either smartphones or tablets by 2017. 8
1. http://newsroom.fb.com/Key-Facts
2. http://www.socialbakers.com/blog/38-top-10-countries-on-facebook-in-the-last-six-months
4. http://www.alexa.com/siteinfo/pinterest.com
5. https://about.twitter.com/company
6. http://www.alexa.com/siteinfo/qq.com
7. http://mashable.com/2012/02/03/smartphone-sales-overtake-pcs/
Wearable
The average smartphone user looks at his or her smartphone 150 times a day for functions such as messaging (23 times), phone calls (22), listening to music (13), and social media (9).9 Many of these functions would be much better served if the technology was worn on, or even physically integrated into, our bodies. This technology is known as a “wearable.”
Wearables have been around for a long time, with technologies such as hearing aids and, later, bluetooth earpieces. But now, we are seeing an explosion of new wearable technologies. Perhaps the best known of these is Google Glass, an augmented reality device that you wear over your eyes like a pair of eyeglasses. Visible only to you, Google Glass will project images into your field of vision based on your context and voice commands. You can find out much more about Google Glass at http://www.google.com/glass/start/.
Another class of wearables are those related to health care. The UP by Jawbone consists of a wristband and an app that tracks how you sleep,
Google Glass. (CC- BY: Flickr, user Tedeytan)
move, and eat, then helps you use that information to feel your best. 10 It can be used to track your sleep
patterns, moods, eating patterns, and other aspects of daily life, and then report back to you via an app on your smartphone or tablet. As our population ages and technology continues to evolve, there will be a large increase in wearables like this.
Collaborative
As more of us use smartphones and wearables, it will be simpler than ever to share data with each other for mutual benefit. Some of this sharing can be done passively, such as reporting our location in order to update traffic statistics. Other data can be reported actively, such as adding our rating of a restaurant to a review site.
The smartphone app Waze is a community-based tool that keeps track of the route you are traveling and how fast you are making your way to your destination. In return for providing your data, you can benefit from the data being sent from all of the other users of the app. Waze will route you around traffic and accidents based upon real-time reports from other users.
Yelp! allows consumers to post ratings and reviews of local businesses into a database, and then it provides that data back to consumers via its website or mobile phone app. By compiling ratings of restaurants, shopping centers, and services, and then allowing consumers to search through its directory, Yelp! has become a huge source of business for many companies. Unlike data collected passively however, Yelp! relies on its users to take the time to provide honest ratings and reviews.
9. http://communities-dominate.blogs.com/brands/2013/03/the-annual-mobile-industry-numbers-and-stats-blog-yep-this-year-we-will-hit-the-mobile-moment.html
10. https://jawbone.com/up
Printable
One of the most amazing innovations to be developed recently is the 3-D printer. A 3-D printer allows you to print virtually any 3-D object based on a model of that object designed on a computer. 3-D printers work by creating layer upon layer of the model using malleable materials, such as different types of glass, metals, or even wax.
3-D printing is quite useful for prototyping the designs of products to determine their feasibility and marketability. 3-D printing has also been used to create working prosthetic legs, handguns, and even an ear that can hear beyond the range of normal hearing. The US Air Force now uses 3-D printed parts on the F-18 fighter jet.11
3-D printing is one of many technologies embraced by the “maker” movement. Chris Anderson, editor of Wired magazine, puts it this way12:
In a nutshell, the term “Maker” refers to a new category of builders who are using open-source methods and the latest technology to bring manufacturing out of its traditional factory context, and into the realm of the personal desktop computer. Until recently, the ability to manufacture was reserved for those who owned factories. What’s happened over the last five years is that we’ve brought the Web’s democratizing power to manufacturing. Today, you can manufacture with the push of a button.
Findable
The “Internet of Things” refers to the idea of physical objects being connected to the Internet. Advances in wireless technologies and sensors will allow physical objects to send and receive data about themselves. Many of the technologies to enable this are already available – it is just a matter of integrating them together.
In a 2010 report by McKinsey & Company on the Internet of Things13, six broad applications are identified:
• Tracking behavior. When products are embedded with sensors, companies can track the movements of these products and even monitor interactions with them. Business models can be fine-tuned to take advantage of this behavioral data. Some insurance companies, for example, are offering to install location sensors in customers’ cars. That allows these companies to base the price of policies on how a car is driven as well as where it travels.
• Enhanced situational awareness. Data from large numbers of sensors deployed, for example, in infrastructure (such as roads and buildings), or to report on environmental conditions (including soil moisture, ocean currents, or weather), can give decision makers a heightened awareness of real-time events, particularly when the sensors are used with advanced display or visualization technologies. Security personnel, for instance, can use sensor networks that combine video, audio, and vibration detectors to spot unauthorized individuals who enter restricted areas.
12. Makers: The New Industrial Revolution by Chris Anderson. Crown Business; 2012.
13. http://www.mckinsey.com/insights/high_tech_telecoms_internet/the_internet_of_things
• Sensor-driven decision analysis. The Internet of Things also can support longer-range, more complex human planning and decision making. The technology requirements – tremendous storage and computing resources linked with advanced software systems that generate a variety of graphical displays for analyzing data – rise accordingly.
• Process optimization. Some industries, such as chemical production, are installing legions of sensors to bring much greater granularity to monitoring. These sensors feed data to computers, which in turn analyze the data and then send signals to actuators that adjust processes – for example, by modifying ingredient mixtures, temperatures, or pressures.
• Optimized resource consumption. Networked sensors and automated feedback mechanisms can change usage patterns for scarce resources, such as energy and water. This can be accomplished by dynamically changing the price of these goods to increase or reduce demand.
• Complex autonomous systems. The most demanding use of the Internet of Things involves the rapid, real-time sensing of unpredictable conditions and instantaneous responses guided by automated systems. This kind of machine decision-making mimics human reactions, though at vastly enhanced performance levels. The automobile industry, for instance, is stepping up the development of systems that can detect imminent collisions and take evasive action.
Autonomous
A final trend that is emerging is an extension of the Internet of Things: autonomous robots and vehicles. By combining software, sensors, and location technologies, devices that can operate themselves to perform specific functions are being developed. These take the form of creations such as medical nanotechnology robots (nanobots), self-driving cars, or unmanned aerial vehicles (UAVs).
A nanobot is a robot whose components are on the scale of about a nanometer, which is one-billionth
of a meter. While still an emerging field, it is showing promise for applications in the medical field. For example, a set of nanobots could be introduced into the human body to combat cancer or a specific disease. In March of 2012, Google introduced the world to their driverless car by showing a blind man driving the car around the San Francisco area. The car combines several technologies, including a laser radar system, worth about $150,000. While the car is not available commercially yet, three
US states (Nevada, Florida, and California) have already passed legislation making driverless cars legal.
A UAV, often referred to as a “drone,” is a small airplane or helicopter that can fly without a pilot. Instead of a pilot, they are either run autonomously by computers in the vehicle or operated by a person using a remote control. While most drones today are used for military or civil applications, there is a growing market for personal drones. For around $300, a consumer can purchase a drone for personal use.
Summary
As the world of information technology moves forward, we will be constantly challenged by new capabilities and innovations that will both amaze and disgust us. As we learned in chapter 12, many times the new capabilities and powers that come with these new technologies will test us and require a new way
of thinking about the world. Businesses and individuals alike need to be aware of these coming changes and prepare for them.
Study Questions
1. Which countries are the biggest users of the Internet? Social media? Mobile?
2. Which country had the largest Internet growth (in %) between 2008 and 2012?
3. How will most people connect to the Internet in the future?
4. What are two different applications of wearable technologies?
5. What are two different applications of collaborative technologies?
6. What capabilities do printable technologies have?
7. How will advances in wireless technologies and sensors make objects “findable”?
8. What is enhanced situational awareness?
9. What is a nanobot?
10. What is a UAV?
Exercises
1. If you were going to start a new technology business, which of the emerging trends do you think would be the biggest opportunity? Do some original research to estimate the market size.
2. What privacy concerns could be raised by collaborative technologies such as Waze?
3. Do some research about the first handgun printed using a 3-D printer and report on some of the concerns raised.
4. Write up an example of how the Internet of Things might provide a business with a competitive advantage.
5. How do you think wearable technologies could improve overall healthcare?
6. What potential problems do you see with a rise in the number of driverless cars? Do some independent research and write a two-page paper that describes where driverless cars are legal and what problems may occur.
7. Seek out the latest presentation by Mary Meeker on “Internet Trends” (if you cannot find it, the video from 2013 is available at http://allthingsd.com/20130529/mary-meekers-2013-internet- trends-deck-the-full-video/). Write a one-page paper describing what the top three trends are, in your opinion.
Answers to Study Questions
Chapter 1
1. What are the five components that make up an information system?
a. hardware, software, data, people, process
2. What are three examples of information system hardware?
a. There are a number of possible answers: a PC, a printer, a mouse, tablets, mobile phones, etc.
3. Microsoft Windows is an example of which component of information systems?
a. It is an operating system, which is a part of the software component.
4. What is application software?
a. Software that does something useful.
5. What roles do people play in information systems?
a. The text includes examples such as helpdesk support, systems analyst, programmer, and
CIO.
6. What is the definition of a process?
a. A process is a series of steps undertaken to achieve a desired outcome or goal.
7. What was invented first, the personal computer or the Internet (ARPANET)?
a. The Internet was activated in 1969; the personal computer was introduced in 1975.
8. In what year were restrictions on commercial use of the Internet first lifted? When were eBay and Amazon founded?
a. Restrictions were lifted in 1991, Amazon was founded in 1994, and eBay was founded in 1995.
9. What does it mean to say we are in a “post-PC world”?
a. The personal computer will no longer be the primary way that people interact and do business.
10. What is Carr’s main argument about information technology?
a. That information technology is just a commodity and cannot be used to gain a competitive advantage.
Chapter 2
1. Write your own description of what the term information systems hardware means.
a. Answers will vary, but should say something about information systems hardware consisting of the physical parts of computing devices that can actually be touched.
2. What is the impact of Moore’s Law on the various hardware components described in this chapter?
a. The student should pick one of the components and discuss the impact of the fact that computing doubles in speed every two years. Most devices are getting smaller, faster, cheaper, and this should be indicated in the answer.
3. Write a summary of one of the items linked to in the “Integrated Computing” section.
a. The student should write a summary of one of the linked articles.
Answers to Study Questions 151
4. Explain why the personal computer is now considered a commodity.
a. The PC has become a commodity in the sense that there is very little differentiation between computers, and the primary factor that controls their sale is their price.
5. The CPU can also be thought of as the of the computer.
a. brain
6. List the following in increasing order (slowest to fastest): megahertz, kilohertz, gigahertz.
a. kilohertz, megahertz, gigahertz
7. What is the bus of a computer?
a. The bus is the electrical connection between different computer components.
8. Name two differences between RAM and a hard disk.
a. RAM is volatile; the hard disk is non-volatile. Data access in RAM is faster than on the hard disk.
9. What are the advantages of solid-state drives over hard disks?
a. The main advantage is speed: an SSD has much faster data-access speeds than a traditional hard disk.
10. How heavy was the first commercially successful portable computer?
a. The Compaq PC was 28 pounds.
Chapter 3
1. Come up with your own definition of software. Explain the key terms in your definition.
a. A variety of answers are possible, but should be similar to the definition in the text: Software is the set of instructions that tell the hardware what to do. Software is created through the process of programming.
2. What are the functions of the operating system?
a. The operating system manages the hardware resources of the computer, provides the user-interface components, and provides a platform for software developers to write applications.
3. Which of the following are operating systems and which are applications: Microsoft Excel, Google Chrome, iTunes, Windows, Android, Angry Birds.
a. Microsoft Excel (application), Google Chrome (application), iTunes (application), WIndows (operating system), Android (operating system), Angry Birds (application)
4. What is your favorite software application? What tasks does it help you accomplish?
a. Students will have various answers to this question. They should pick an application, not an operating system. They should be able to list at least one thing that it helps them accomplish.
5. What is a “killer” app? What was the killer app for the PC?
a. A killer app is application software that is so useful that people will purchase the hardware just so they can run it. The killer app for the PC was the spreadsheet (Visicalc).
6. How would you categorize the software that runs on mobile devices? Break down these apps into at least three basic categories and give an example of each.
a. There are various ways to answer this question. Students should identify that there are mobile operating systems and mobile apps. Most likely, students will break down mobile apps into multiple categories: games, GPS, reading, communication, etc.
7. Explain what an ERP system does.
a. An ERP (enterprise resource planning) system is a software application with a centralized database that is implemented across the entire organization.
152 Information Systems for Business and Beyond
8. What is open-source software? How does it differ from closed-source software? Give an example of each.
a. Open-source software is software that makes the source code available for anyone to copy and use. It is free to download, copy, and distribute. Closed-source software does not make the source code available and generally is not free to download, copy, and distribute. There are many examples of both, such as: Firefox (open source), Linux (open source), iTunes (closed source), Microsoft Office (closed source).
9. What does a software license grant?
a. Software licenses are not all the same, but generally they grant the user the right to use the software on a limited basis. The terms of the license dictate users’ rights in detail.
10. How did the Y2K (year 2000) problem affect the sales of ERP systems?
a. Organizations purchased ERP software to replace their older systems in order to avoid any problems with the year 2000 in their software.
Chapter 4
1. What is the difference between data, information, and knowledge?
a. Data are the raw bits and pieces of facts and statistics with no context. Data can be quantitative or qualitative. Information is data that has been given context. Knowledge is information that has been aggregated and analyzed and can be used for making decisions.
2. Explain in your own words how the data component relates to the hardware and software components of information systems.
a. There are numerous answers to this question, but all should be variations on the following: Data is processed by the hardware via software. A database is software that runs on the hardware. Hardware stores the data, software processes the data.
3. What is the difference between quantitative data and qualitative data? In what situations could the number 42 be considered qualitative data?
a. Quantitative data is numeric, the result of a measurement, count, or some other mathematical calculation. Qualitative data is descriptive. The number 42 could be qualitative if it is a designation instead of a measurement, count, or calculation. For example: that player’s jersey has number 42 on it.
4. What are the characteristics of a relational database?
a. A relational database is one in which data is organized into one or more tables. Each table has a set of fields, which define the nature of the data stored in the table. A record is one instance of a set of fields in a table. All the tables are related by one or more fields in common.
5. When would using a personal DBMS make sense?
a. When working on a smaller database for personal use, or when disconnected from the network.
6. What is the difference between a spreadsheet and a database? List three differences between them.
a. A database is generally more powerful and complex than a spreadsheet, with the ability to handle multiple types of data and link them together. Some differences: A database has defined field types, a spreadsheet does not. A database uses a standardized query language (such as SQL), a spreadsheet does not. A database can hold much larger amounts of data than a spreadsheet.
7. Describe what the term normalization means.
Answers to Study Questions 153
a. To normalize a database means to design it in a way that: 1) reduces duplication of data between tables and 2) gives the table as much flexibility as possible.
8. Why is it important to define the data type of a field when designing a relational database?
a. A data type tells the database what functions can be performed with the data. The second important reason to define the data type is so that the proper amount of storage space is allocated for the data.
9. Name a database you interact with frequently. What would some of the field names be?
a. The student can choose any sort of system that they interact with, such as Amazon or their school’s online systems. The fields would be the names of data being collected, such as “first name”, or “address”.
10. What is metadata?
a. Metadata is data about data. It refers to the data used to describe other data, such as the length of a song in iTunes, which describes the music file.
11. Name three advantages of using a data warehouse.
a. The text lists the following (the student should pick at least three of these):
i. The process of developing a data warehouse forces an organization to better understand the data that it is currently collecting and, equally important, what data is not being collected.
ii. A data warehouse provides a centralized view of all data being collected across the enterprise and provides a means of determining data that is inconsistent.
iii. Once all data is identified as consistent, an organization can generate one version of the truth. This is important when the company wants to report consistent statistics about itself, such as revenue or number of employees.
iv. By having a data warehouse, snapshots of data can be taken over time. This creates a historical record of data, which allows for an analysis of trends.
v. A data warehouse provides tools to combine data, which can provide new information and analysis.
12. What is data mining?
a. Data mining is the process of analyzing data to find previously unknown trends, patterns, and associations in order to make decisions.
Chapter 5
1. What were the first four locations hooked up to the Internet (ARPANET)?
a. UCLA, Stanford, MIT, and the University of Utah
2. What does the term packet mean?
a. The fundamental unit of data transmitted over the Internet. Each packet has the sender’s address, the destination address, a sequence number, and a piece of the overall message to be sent.
3. Which came first, the Internet or the World Wide Web?
a. the Internet
4. What was revolutionary about Web 2.0?
a. Anyone could post content to the web, without the need for understanding HTML or web- server technology.
5. What was the so-called killer app for the Internet?
a. electronic mail (e-mail)
6. What makes a connection a broadband connection?
154 Information Systems for Business and Beyond
a. A broadband connection is defined as one that has speeds of at least 256,000 bps.
7. What does the term VoIP mean?
a. Voice over Internet protocol – a way to have voice conversations over the Internet.
8. What is an LAN?
a. An LAN is a local network, usually operating in the same building or on the same campus.
9. What is the difference between an intranet and an extranet?
a. An intranet consists of the set of web pages and resources available on a company’s internal network. These items are not available to those outside of the company. An extranet is a part of the company’s network that is made available securely to those outside of the company. Extranets can be used to allow customers to log in and check the status of their orders, or for suppliers to check their customers’ inventory levels.
10. What is Metcalfe’s Law?
a. Metcalfe’s Law states that the value of a telecommunications network is proportional to the square of the number of connected users of the system.
Chapter 6
1. Briefly define each of the three members of the information security triad.
a. The three members are as follows:
i. Confidentiality: we want to be able to restrict access to those who are allowed to see given information.
ii. Integrity: the assurance that the information being accessed has not been altered and truly represents what is intended.
iii. Availability: information can be accessed and modified by anyone authorized to do so in an appropriate timeframe.
2. What does the term authentication mean?
a. The process of ensuring that a person is who he or she claims to be.
3. What is multi-factor authentication?
a. The use of more than one method of authentication. The methods are: something you know, something you have, and something you are.
4. What is role-based access control?
a. With role-based access control (RBAC), instead of giving specific users access rights to an information resource, users are assigned to roles and then those roles are assigned the access.
5. What is the purpose of encryption?
a. To keep transmitted data secret so that only those with the proper key can read it.
6. What are two good examples of a complex password?
a. There are many examples of this. Students need to provide examples of passwords that are a minimum of eight characters, with at least one upper-case letter, one special character, and one number.
7. What is pretexting?
a. Pretexting occurs when an attacker calls a helpdesk or security administrator and pretends to be a particular authorized user having trouble logging in. Then, by providing some personal information about the authorized user, the attacker convinces the security person to reset the password and tell him what it is.
8. What are the components of a good backup plan?
Answers to Study Questions 155
a. Knowing what needs to be backed up, regular backups of all data, offsite storage of all backed-up data, and a test of the restoration process.
9. What is a firewall?
a. A firewall can be either a hardware firewall or a software firewall. A hardware firewall is a device that is connected to the network and filters the packets based on a set of rules. A software firewall runs on the operating system and intercepts packets as they arrive to a computer.
10. What does the term physical security mean?
a. Physical security is the protection of the actual hardware and networking components that store and transmit information resources.
Chapter 7
1. What is the productivity paradox?
a. The productivity paradox is based on Erik Brynjolfsson’s finding, based on research he conducted in the early 1990s, that the addition of information technology to business had not improved productivity at all.
2. Summarize Carr’s argument in “Does IT Matter.”
a. Information technology is now a commodity and cannot be used to provide an organization with competitive advantage.
3. How is the 2008 study by Brynjolfsson and McAfee different from previous studies? How is it the same?
a. It is different because it shows that IT can bring a competitive advantage, given the right conditions. It is the same in the sense that it shows that IT, by itself, does not bring competitive advantage.
4. What does it mean for a business to have a competitive advantage?
a. A company is said to have a competitive advantage over its rivals when it is able to sustain profits that exceed average for the industry.
5. What are the primary activities and support activities of the value chain?
a. The primary activities are those that directly impact the creation of a product or service. The support activities are those that support the primary activities. Primary: inbound logistics, operations, outbound logistics, sales/marketing, and service. Support: firm infrastructure, human resources, technology development, and procurement.
6. What has been the overall impact of the Internet on industry profitability? Who has been the true winner?
a. The overall impact has been a reduction in average industry profitability. The consumer has been the true winner.
7. How does EDI work?
a. EDI is the computer-to-computer exchange of business documents in a standard electronic format between business partners.
8. Give an example of a semi-structured decision and explain what inputs would be necessary to provide assistance in making the decision.
a. A semi-structured decision is one in which most of the factors needed for making the decision are known but human experience and other outside factors may still play a role. The student should provide an example of a decision that uses an information system to provide information but is not made by the system. Examples would include: budgeting decisions, diagnosing a medical condition, and investment decisions.
9. What does a collaborative information system do?
156 Information Systems for Business and Beyond
a. A collaborative system is software that allows multiple users to interact on a document or topic in order to complete a task or make a decision.
10. How can IT play a role in competitive advantage, according to the 2008 article by Brynjolfsson and McAfee?
a. The article suggests that IT can influence competitive advantage when good management develops and delivers IT-supported process innovation.
Chapter 8
1. What does the term business process mean?
a. A process is a series of tasks that are completed in order to accomplish a goal. A business process, therefore, is a process that is focused on achieving a goal for a business.
2. What are three examples of business process from a job you have had or an organization you have observed?
a. Students can answer this in almost any way. The examples should consist of more than a single step.
3. What is the value in documenting a business process?
a. There are many answers to this. From the text: it allows for better control of the process, and for standardization.
4. What is an ERP system? How does an ERP system enforce best practices for an organization?
a. An ERP (enterprise resource planning) system is a software application with a centralized database that is implemented across the entire organization. It enforces best practices through the business processes embedded in the software.
5. What is one of the criticisms of ERP systems?
a. ERP systems can lead to the commoditization of business processes, meaning that every company that uses an ERP system will perform business processes the same way.
6. What is business process reengineering? How is it different from incrementally improving a process?
a. Business process reengineering (BPR) occurs when a business process is redesigned from the ground up. It is different from incrementally improving a process in that it does not simply take the existing process and modify it.
7. Why did BPR get a bad name?
a. BPR became an excuse to lay off employees and try to complete the same amount of work using fewer employees.
8. List the guidelines for redesigning a business process.
a. The guidelines are as follows:
i. Organize around outcomes, not tasks.
ii. Have those who use the outcomes of the process perform the process.
iii. Subsume information-processing work into the real work that produces the information. Treat geographically dispersed resources as though they were centralized.
iv. Link parallel activities instead of integrating their results.
v. Put the decision points where the work is performed, and build controls into the process.
vi. Capture information once, at the source.
9. What is business process management? What role does it play in allowing a company to differentiate itself?
Answers to Study Questions 157
a. Business process management (BPM) can be thought of as an intentional effort to plan, document, implement, and distribute an organization’s business processes with the support of information technology. It can play a role in differentiation through built-in reporting, and by empowering employees, enforcing best practices, and enforcing consistency.
10. What does ISO certification signify?
a. ISO certification shows that you know what you do, do what you say, and have documented your processes.
Chapter 9
1. Describe the role of a systems analyst.
a. To understand business requirements and translate them into the requirements of an information system.
2. What are some of the different roles for a computer engineer?
a. hardware engineer, software engineer, network engineer, systems engineer
3. What are the duties of a computer operator?
a. Duties include keeping the operating systems up to date, ensuring available memory and disk storage, and overseeing the physical environment of the computer.
4. What does the CIO do?
a. The CIO aligns the plans and operations of the information systems with the strategic goals of the organization. This includes tasks such as budgeting, strategic planning, and personnel decisions relevant to the information-systems function.
5. Describe the job of a project manager.
a. A project manager is responsible for keeping projects on time and on budget. This person works with the stakeholders of the project to keep the team organized and communicates the status of the project to management.
6. Explain the point of having two different career paths in information systems.
a. To allow for career growth for those who do not want to manage other employees but instead want to focus on technical skills.
7. What are the advantages and disadvantages of centralizing the IT function?
a. There are several possible answers here. Advantages of centralizing include more control over the company’s systems and data. Disadvantages include a more limited availability of IT resources.
8. What impact has information technology had on the way companies are organized?
a. The organizational structure has been flattened, with fewer layers of management.
9. What are the five types of information-systems users?
a. innovators, early adopters, early majority, late majority, laggards
10. Why would an organization outsource?
a. Because it needs a specific skill for a limited amount of time, and/or because it can cut costs by outsourcing.
Chapter 10
1. What are the steps in the SDLC methodology?
a. The steps are Preliminary Analysis, System Analysis, System Design, Programming, Testing, Implementation, and Maintenance.
2. What is RAD software development?
158 Information Systems for Business and Beyond
one?
a. Rapid application development (RAD) is a software-development (or systems- development) methodology that focuses on quickly building a working model of the software, getting feedback from users, and then using that feedback to update the working model.
3. What makes the lean methodology unique?
a. The biggest difference between the lean methodology and the other methodologies is that the full set of requirements for the system is not known when the project is launched.
4. What are three differences between second-generation and third-generation languages?
a. Three key differences are as follows:
i. The words used in the language: third generation languages use more English- like words than second-generation languages.
ii. Hardware specificity: third generation languages are not specific to hardware, second-generation languages are.
iii. Learning curve: third generation languages are easier to learn and use.
5. Why would an organization consider building its own software application if it is cheaper to buy
a. They may wish to build their own in order to have something that is unique (different from their competitors), and/or something that more closely matches their business processes. They also may choose to do this if they have more time and/or more money available to do it.
6. What is responsive design?
a. Responsive design is a method of developing websites that allows them to be viewed on many different types of devices without losing capability or effectiveness. With a responsive website, images resize themselves based on the size of the device’s screen, and text flows and sizes itself properly for optimal viewing.
7. What is the relationship between HTML and CSS in website design?
a. While HTML is used to define the components of a web page, cascading style sheets (CSS) are used to define the styles of the components on a page.
8. What is the difference between the pilot implementation methodology and the parallel
implementation methodology?
a. The pilot methodology implements new software for just one group of people while the rest of the users use the previous version of the software. The parallel implementation methodology uses both the old and the new applications at the same time.
9. What is change management?
a. The oversight of the changes brought about in an organization.
10. What are the four different implementation methodologies?
a. direct cutover, pilot, parallel, phased
Chapter 11
1. What does the term globalization mean?
a. Globalization refers to the integration of goods, services, and cultures among the nations of the world.
2. How does Friedman define the three eras of globalization?
a. The three eras are as follows:
i. “Globalization 1.0” occurred from 1492 until about 1800. In this era, globalization was centered around countries. It was about how much horsepower, wind power, and steam power a country had and how creatively it was deployed. The world shrank from size “large” to size “medium.”
Answers to Study Questions 159
ii. “Globalization 2.0” occurred from about 1800 until 2000, interrupted only by the two World Wars. In this era, the dynamic force driving change was comprised of multinational companies. The world shrank from size “medium” to size “small.”
iii. “Globalization 3.0” is our current era, beginning in the year 2000. The convergence of the personal computer, fiber-optic Internet connections, and software has created a “flat-world platform” that allows small groups and even individuals to go global. The world has shrunk from size “small” to size “tiny.”
3. Which technologies have had the biggest effect on globalization?
a. There are several answers to this. Probably the most obvious are the Internet, the graphical interface of Windows and the World Wide Web, and workflow software.
4. What are some of the advantages brought about by globalization?
a. Advantages include the ability to locate expertise and labor around the world, the ability to operate 24 hours a day, and a larger market for products.
5. What are the challenges of globalization?
a. Challenges include infrastructure differences, labor laws and regulations, legal restrictions, and different languages, customs, and preferences.
6. What does the term digital divide mean?
a. The separation between those who have access to the global network and those who do not. The digital divide can occur between countries, regions, or even neighborhoods.
7. What are Jakob Nielsen’s three stages of the digital divide?
a. economic, usability, and empowerment
8. What was one of the key points of The Rise of the Network Society?
a. There are two key points to choose from. One is that economic activity was, when the book was published in 1996, being organized around the networks that the new telecommunication technologies had provided. The other is that this new, global economic activity was different from the past, because “it is an economy with the capacity to work as a unit in real time on a planetary scale.”
9. Which country has the highest average Internet speed? How does your country compare?
a. According to the chart in the chapter, South Korea has the highest Internet speeds. Students will need to look up their own to compare.
10. What is the OLPC project? Has it been successful?
a. One Laptop Per Child. By most measures, it has not been a successful program.
Chapter 12
1. What does the term information systems ethics mean?
a. There are various ways of answering this question, but the answer should include something about the application of ethics to the new capabilities and cultural norms brought about by information technology.
2. What is a code of ethics? What is one advantage and one disadvantage of a code of ethics?
a. A code of ethics is a document that outlines a set of acceptable behaviors for a professional or social group. Answers may differ for the second part, but from the text: one advantage of a code of ethics is that it clarifies the acceptable standards of behavior for a professional group. One disadvantage is that it does not necessarily have legal authority.
3. What does the term intellectual property mean? Give an example.
a. Intellectual property is defined as “property (as an idea, invention, or process) that derives from the work of the mind or intellect.”
160 Information Systems for Business and Beyond
4. What protections are provided by a copyright? How do you obtain one?
a. Copyright protections address the following: who can make copies of the work, who can make derivative works from the original work, who can perform the work publicly, who can display the work publicly, and who can distribute the work. You obtain a copyright as soon as the work is put into tangible form.
5. What is fair use?
a. Fair use is a limitation on copyright law that allows for the use of protected works without prior authorization in specific cases.
6. What protections are provided by a patent? How do you obtain one?
a. Once a patent is granted, it provides the inventor with protection from others infringing on the patent. In the US, a patent holder has the right to “exclude others from making, using, offering for sale, or selling the invention throughout the United States or importing the invention into the United States for a limited time in exchange for public disclosure of the invention when the patent is granted.” You obtain a patent by filing an application with the patent office. A patent will be granted if the work is deemed to be original, useful, and non-obvious.
7. What does a trademark protect? How do you obtain one?
a. A trademark protects a word, phrase, logo, shape, or sound that identifies a source of goods or services. You can obtain one by registering with the Patent and Trademark Office (US). There is also a common-law trademark.
8. What does the term personally identifiable information mean?
a. Information about a person that can be used to uniquely establish that person’s identity is called personally identifiable information, or PII.
9. What protections are provided by HIPAA, COPPA, and FERPA?
a. The answers are as follows:
i. HIPAA: protects records related to health care as a special class of personally identifiable information.
ii. COPPA: protects information collected from children under the age of thirteen.
iii. FERPA: protects student educational records.
10. How would you explain the concept of NORA?
a. There are various ways to answer this. The basic answer is that NORA (non-obvious relationship awareness) is the process of collecting large quantities of a variety of information and then combining it to create profiles of individuals.
Chapter 13
1. Which countries are the biggest users of the Internet? Social media? Mobile?
a. Students will need to look outside the text for this, as it changes all the time. There are also different ways of measurement: number of users, % of population, most active users, etc. Some good sites to use are Internet World Stats, Kissmetrics, and the World Bank.
2. Which country had the largest Internet growth (in %) between 2008 and 2012?
a. Iran, at 205%
3. How will most people connect to the Internet in the future?
a. via mobile devices
4. What are two different applications of wearable technologies?
a. There are many answers to this question; two examples are Google Glass and Jawbone
UP.
5. What are two different applications of collaborative technologies?
Answers to Study Questions 161
a. There are many answers to this; two examples are software that routes us to our destination in the shortest amount of time, and websites that review different companies.
6. What capabilities do printable technologies have?
a. Using 3-D printers, designers can quickly test prototypes or build something as a proof of concept. Printable technologies also make it possible to bring manufacturing to the desktop computer.
7. How will advances in wireless technologies and sensors make objects “findable”?
a. Advances in wireless technologies and sensors will allow physical objects to send and receive data about themselves.
8. What is enhanced situational awareness?
a. Data from large numbers of sensors can give decision makers a heightened awareness of real-time events, particularly when the sensors are used with advanced display or visualization technologies.
9. What is a nanobot?
a. A nanobot is a robot whose components are on the scale of about a nanometer.
10. What is a UAV?
a. An unmanned aerial vehicle – a small airplane or helicopter that can fly without a pilot. UAVs are run by computer or remote control.
Anderson, Chris. Makers: The New Industrial Revolution. New York: Crown Business, 2012.
Brynjolfsson, Erik. “The Productivity Paradox of Information Technology: Review and Assessment.” Communications of the ACM, December, 1993. http://ccs.mit.edu/papers/CCSWP130/ ccswp130.html.
Brynjolfsson, Erik and Lorin Hitt. “Beyond the Productivity Paradox: Computers are the Catalyst for Bigger Changes.” Communications of the ACM, August 1998, vol. 41(8): pp. 49–55. http://ebusiness.mit.edu/erik/bpp.pdf
Castells, Manuel. The Rise of the Network Society. 2nd ed. Cambridge, MA: Blackwell Publishers, 2000.Valacich, Joseph, and Christoph Schneider. Information Systems Today: Managing in the Digital World. 4th ed. Upper Saddle River, NJ: Prentice-Hall, 2010.
Chui, Michael, Markus Löffler, and Roger Roberts. “The Internet of Things.” McKinsey Quarterly, March 2010. http://www.mckinsey.com/insights/high_tech_telecoms_internet/the_internet_of_things
Columbus, Louis. “IDC: 87% of Connected Devices Sales by 2017 Will Be Tablets and Smartphones.”
Tech section of forbes.com, September 12, 2013. http://www.forbes.com/sites/louiscolumbus/2013/09/12/ idc-87-of-connected-devices-by-2017-will-be-tablets-and-smartphones/
Friedman, T. L. The World Is Flat: A Brief History of the Twenty-First Century. New York: Farrar, Straus and Giroux, 2005.
Gallagher, Sean. ”Born to Be Breached: The Worst Passwords Are Still the Most Common.” Arstechnica, November 3, 2012. Retrieved from http://arstechnica.com/information- technology/2012/11/born-to-be-breached-the-worst-passwords-are-still-the-most-common/ on May 15, 2013.
Godin, Seth. Really Bad PowerPoint (and How to Avoid It). Do You Zoom, Inc., 2001. http://www.sethgodin.com/freeprize/reallybad-1.pdf.
Guel, Michele D. ”A Short Primer for Developing Security Policies.” SANS Institute, 2007. Accessed from http://www.sans.org/security-resources/policies/Policy_Primer.pdf on May 31, 2013.
Hammer, Michael. “Reengineering Work: Don’t Automate, Obliterate.” Harvard Business Review, 68.4 (1990): 104–112.
Kibum, Kim. “Challenges in HCI: Digital Divide.” Crossroads, vol. 12, issue 2 (December 2005), 2–2, doi: 10.1145/1144375.1144377. http://doi.acm.org/10.1145/1144375.1144377.
Kim, P., E. Buckner, T. Makany, and H. Kim. “A Comparative Analysis of a Game-Based Mobile Learning Model in Low-Socioeconomic Communities of India.” International Journal of Educational Development, vol. 32, issue 2 (March 2012), pp. 205–366, doi:10.1016/j.ijedudev.2011.05.008.
Kraemer, Kenneth L., Jason Dedrick, and Prakul Sharma. “One Laptop Per Child: Vision vs.
Reality.” Communications of the ACM, vol. 52, no. 6, pp. 66–73.
Laudon, Kenneth C., and Jane P. Laudon. Management Information Systems: Managing the Digital Firm. 12th ed. Upper Saddle River, NJ: Prentice-Hall, 2012.
McAfee, Andrew and Erik Brynjolfsson. “Investing in the IT That Makes a Competitive Difference.” Harvard Business Review, July-August, 2008.
McCallister, Erika, Tim Grance, and Karen Scarfone. Guide to Protecting the Confidentiality of Personally Identifiable Information (PII). National Institute of Standards and Technology, US Department of Commerce Special Publication 800-122, April 2010. http://csrc.nist.gov/publications/nistpubs/800-122/ sp800-122.pdf
Bibliography 163
Moore, Gordon E. “Cramming More Components onto Integrated Circuits.” Electronics, pp. 114–117, April 19, 1965.
Porter, Michael. “Strategy and the Internet.” Harvard Business Review, vol. 79, no. 3, March 2001. http://hbswk.hbs.edu/item/2165.html
Rogers, E. M. Diffusion of Innovations. New York: Free Press, 1962.
Whitney, Lance. “Smartphone Shipments to Surpass Feature Phones This Year.” CNet, June 4, 2013. http://news.cnet.com/8301-1035_3-57587583-94/smartphone-shipments-to-surpass-feature-phones-this- year/
Wiseman, C., and I. C. MacMillan. “Creating Competitive Weapons from Information
